This is a new report by Pen Test Partners about who is tracking your run through applications, smart devices and services.
Plenty of security vulnerabilities have been found in fitness tracking devices, but we wanted to have a look at the mobile apps that are used for run and bike tracking. Strap your phone to your arm and go out for a run or bike or horse ride. The results were quite shocking.
We found that most of the popular apps we looked at paid scant regard to users security. Default settings encouraged users to over-share personal data. One app had a security flaw that allow private runs to be viewed in real time, so the victim could be tracked.
We looked at this because with these tracking we’re not talking about the risk to a device, or to personal information being harvested, or passwords being stolen. We’re talking about genuine risk to personal safety if that information got into the wrong hands.
Real-time stalking anyone?
Briefly, Nike+ was good. Strava was OK, MapMyRun and RunKeeper were below par and RunTastic had a scary security flaw (now fixed).
What’s at risk?
YOU ARE.
If it’s trivial for anyone to access app data via the website mothership, to target a person and identify exactly where they are (or are going to be) then we have a serious problem on our hands. Of course the availability of that information depends on how a user has configured their app, but as we know many people don’t change default settings. We also know that manufacturers often fail at flagging the importance of changing these settings, and sometimes they don’t provide them at all.
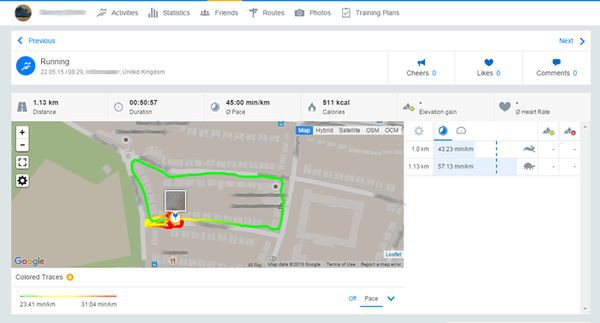
The apps use your phone’s GPS and accelerometers. The information provided is common across all tracking apps. Location, distance, speed, time and elevation are all logged.
Here’s one of us out for a run. During the run, one could watch the runner moving in real time:
In isolation this is fairly harmless information. Athletes have been monitoring this stuff for years, latterly with sports watches. The difference with today is that the information stayed in the watch, it wasn’t sent wirelessly or recorded automatically elsewhere as it is now.
Apps under scrutiny
Bearing all that in mind we thought a security review of the main apps was long overdue. We looked at some of the most popular iOS, Android, Windows Phone, and BlackBerry apps and compared their features and associated security risks. The chosen apps were:
- MapMyRun
- Nike+
- Runkeeper
- Runtastic
- Strava
We limited our investigations to the information sent to and from our phone apps as a regular user. We didn’t reverse engineer the apps or analyse anything server-side.
Read the full article from here.